Discovering the Duty of Universal Cloud Storage Space Providers in Data Protection and Conformity
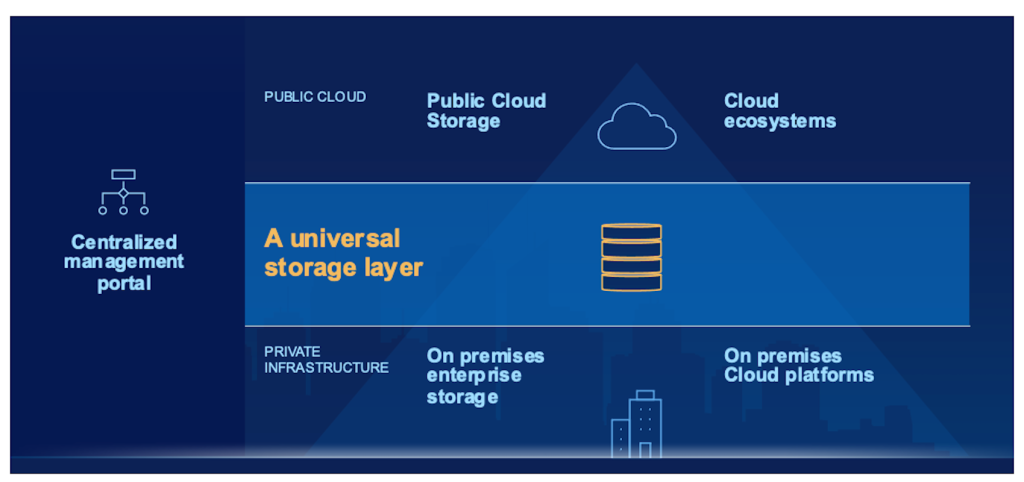
As services significantly depend on cloud storage services to manage and secure their data, discovering the elaborate duty these services play in making sure data safety and security and meeting regulative requirements is crucial. By diving right into the subtleties of universal cloud storage space solutions, a more clear understanding of their influence on data security and regulatory conformity arises, losing light on the intricacies and opportunities that lie in advance.
Importance of Cloud Storage Services
Cloud storage solutions play a pivotal function in modern information management strategies as a result of their scalability, availability, and cost-effectiveness. With the rapid development of data in today's digital age, businesses are significantly turning to shadow storage remedies to meet their evolving requirements. Scalability is a crucial advantage of cloud storage, allowing organizations to conveniently readjust their storage capacity as information demands change. This adaptability ensures that companies can effectively manage their information without the requirement for substantial in advance investments in hardware infrastructure.
Ease of access is another essential aspect of cloud storage space services. By saving data in the cloud, users can access their information from anywhere with a web link, helping with cooperation and remote job. This availability advertises operational efficiency and makes it possible for seamless sharing of information across groups and areas.
Furthermore, many cloud storage suppliers use pay-as-you-go rates versions, allowing companies to pay only for the storage space capability they use. In general, the value of cloud storage services exists in their ability to streamline information monitoring processes, enhance ease of access, and lower functional prices.
Information Protection Approaches With Cloud
Carrying out robust data security methods is crucial for guaranteeing the safety and confidentiality of info kept in cloud atmospheres. File encryption plays an important function in guarding data both en route and at remainder. By securing data before it is submitted to the cloud and preserving control over the encryption tricks, organizations can protect against unauthorized accessibility and reduce the risk of information breaches. Furthermore, executing access controls and authentication systems assists in controlling that can access the information stored in the cloud. Multi-factor verification, strong password plans, and normal access reviews are some approaches that can boost data protection in cloud storage space solutions.
On a regular basis backing up data is an additional important element of data protection in the cloud. By creating back-ups kept in different locations, organizations can guarantee information availability and resilience in situation of unforeseen events such as cyber-attacks, equipment failures, or natural disasters. Performing routine security audits and assessments can help determine susceptabilities and make sure conformity with information defense laws. By integrating encryption, access controls, back-ups, and routine safety and security assessments, organizations can develop a robust data protection method in cloud atmospheres.
Conformity Considerations in Cloud Storage
Provided the essential nature of data protection techniques in cloud atmospheres, organizations have to also prioritize compliance considerations when it pertains to storing information in the cloud. Conformity needs vary across sectors and regions, making it essential for companies to recognize and stick to the relevant laws. When using cloud storage services, services require to ensure that the company adheres to industry-specific requirements such as GDPR, HIPAA, or PCI DSS, depending upon the sort of information being saved. Additionally, companies must think about data residency demands to guarantee that information is stored in compliant locations.
Challenges and Solutions in Cloud Safety
Making certain durable safety procedures in cloud atmospheres offers a diverse obstacle for companies today. One of the key challenges in cloud safety and security is information violations. Malicious stars frequently target cloud systems to obtain unapproved access to sensitive info. To reduce this risk, organizations must apply strong encryption procedures, access controls, and regular safety audits. An additional obstacle is the shared duty design in cloud computing, where both the cloud provider and the client are accountable for different elements of protection. This can cause confusion and spaces in protection coverage if not plainly specified. Organizations has to clearly lay out duties and duties to make certain comprehensive security procedures remain in area.
Future Fads in Cloud Data Defense
The evolving landscape of cloud information protection is marked by a universal cloud storage press release growing emphasis on proactive defense techniques and flexible protection actions (universal cloud storage). As innovation advances and cyber risks end up being a lot more innovative, organizations are increasingly concentrating on predictive analytics, expert system, and artificial intelligence to improve their information security abilities in the cloud
Among the future trends in cloud information defense is the assimilation of automation and orchestration devices to enhance safety and security operations and reaction procedures. By automating routine tasks such as danger detection, occurrence feedback, and spot monitoring, companies can enhance their overall security pose and much better shield their data in the cloud.
Additionally, the adoption of a zero-trust safety model is acquiring grip in the world of cloud data defense. This approach presumes that threats can be both outside and internal, calling for continuous authentication and permission for all customers and tools accessing the cloud setting. By applying a zero-trust framework, organizations can lower the danger of information breaches and unauthorized access to delicate details stored in the cloud.
Final Thought